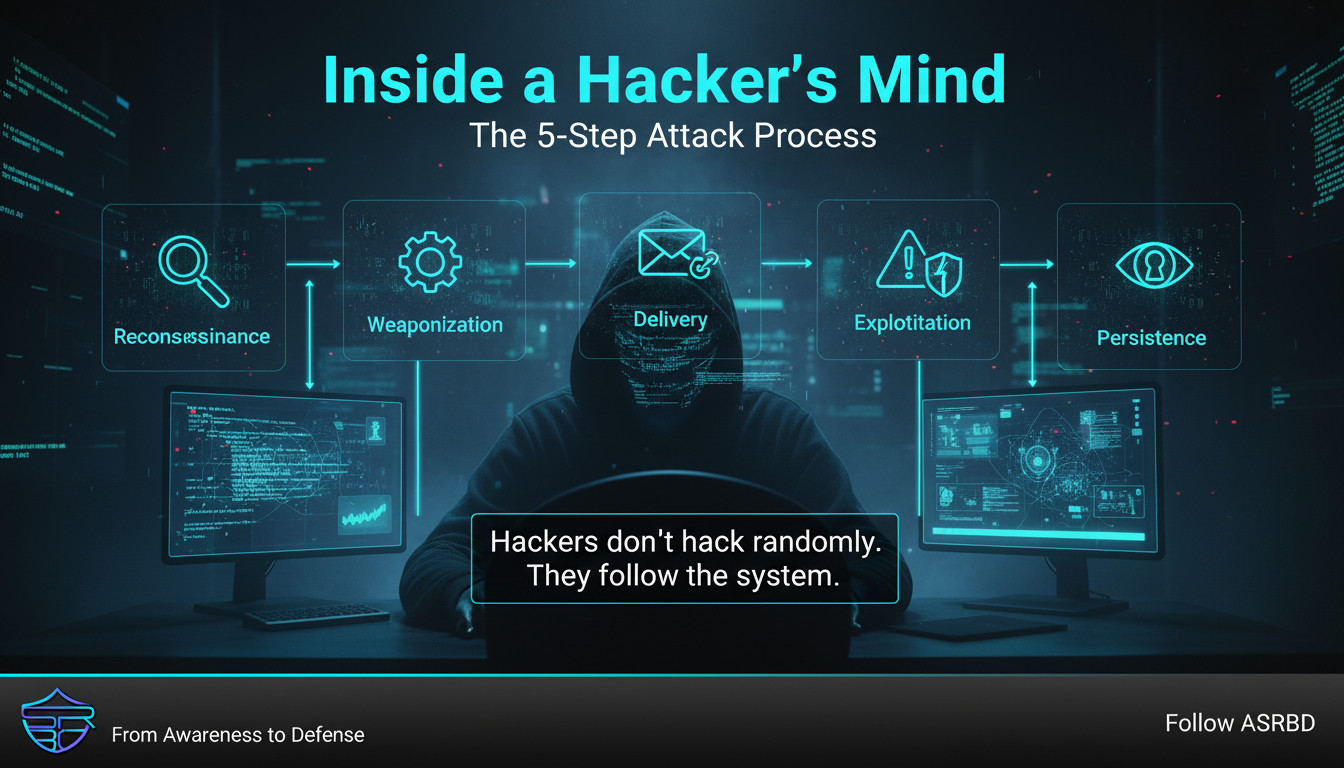
Inside a Hacker’s Mind: The 5-Step Attack Process
🧠 Inside a Hacker’s Mind Most people think hacking is random, chaotic, and unpredictable. But in reality? Hackers follow a structured playbook. Understanding this process is the first step to s...
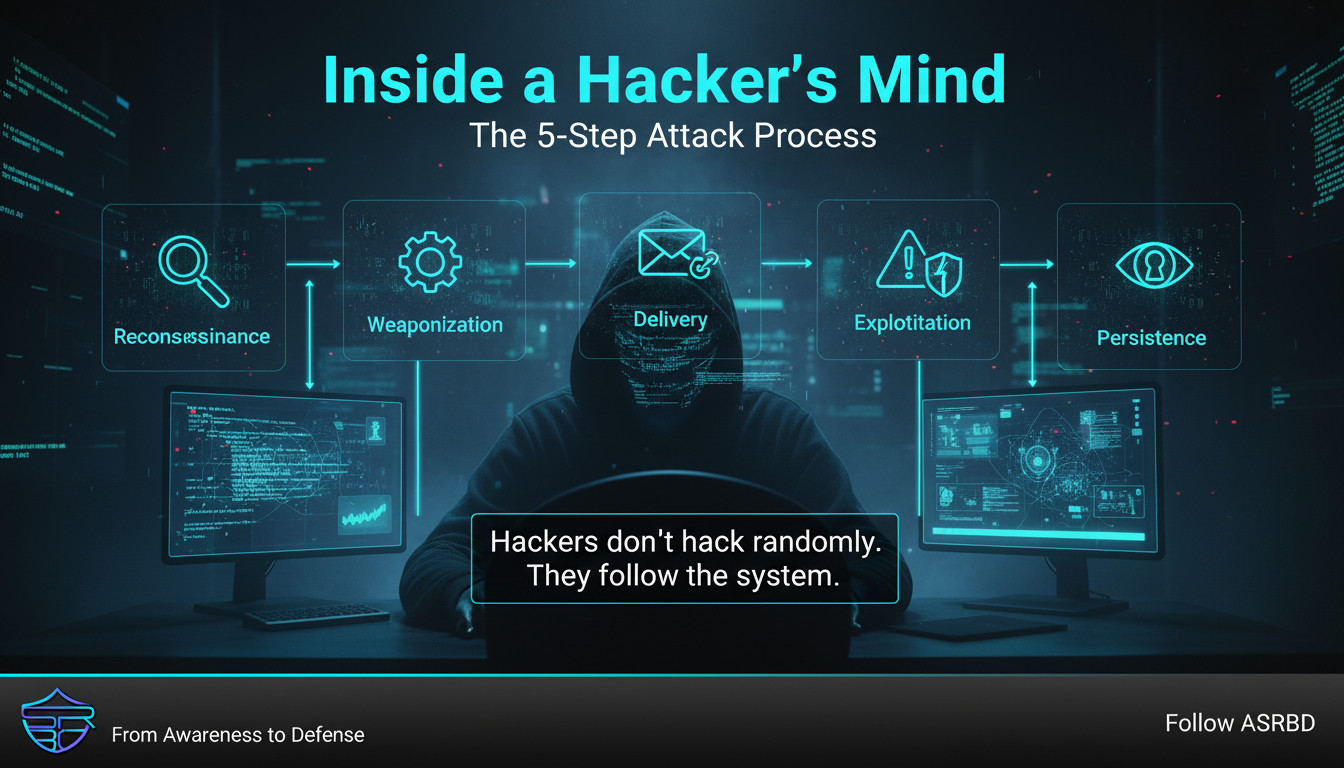
🧠 Inside a Hacker’s Mind Most people think hacking is random, chaotic, and unpredictable. But in reality? Hackers follow a structured playbook. Understanding this process is the first step to s...

Email Spoofing & BEC: The Attack You Can’t See You receive an email. From your boss. From your CEO. “Urgent: Process this payment now.” “Send me the file immediately.” Everything looks ...

☁️ Cloud Account Security: Protect Your Digital Assets Today, our important files, documents, and memories are stored in cloud platforms like Google Drive, Dropbox, and iCloud. While these service...
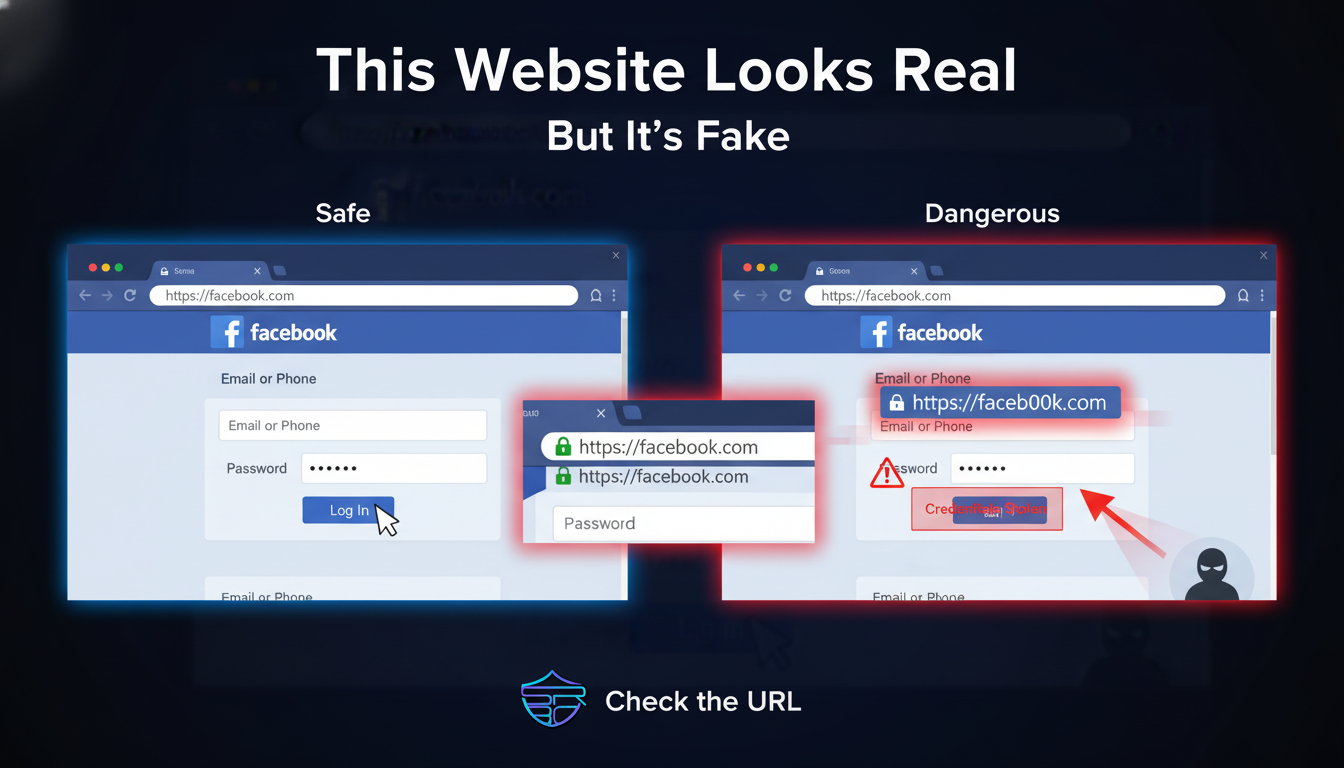
Fake Websites & Domains: How Scammers Trick You You visit a website. It looks exactly like the real one. Same colors Same layout Same login page Nothing feels wrong. 👉 That’s exact...

🏠 Day 15: Home / IoT Device Security Smart devices make our homes more convenient — but every connected device can also become a potential entry point for attackers. From Wi-Fi routers, smart TVs...

SIM Swap Attacks: Don’t Let Hackers Steal Your Phone Number You trust your phone number. It’s connected to: Your bank Your email Your social media But what if someone else takes control ...

🔐 Day 13: Mobile Device Security Smartphones are no longer just communication devices — they store our banking apps, emails, personal photos, social accounts, passwords, and identity data. This m...

What Is a RAT (Remote Access Trojan)? You think your device is private. Your files. Your camera. Your messages. But what if someone else had access to all of it? 👉 That’s exactly what a RAT doe...

🚨 Recognize Scams (Phone/SMS) Phone and SMS scams are rapidly increasing, targeting people through fear, urgency, and deception. Scammers often pretend to be bank officials, government authorities...
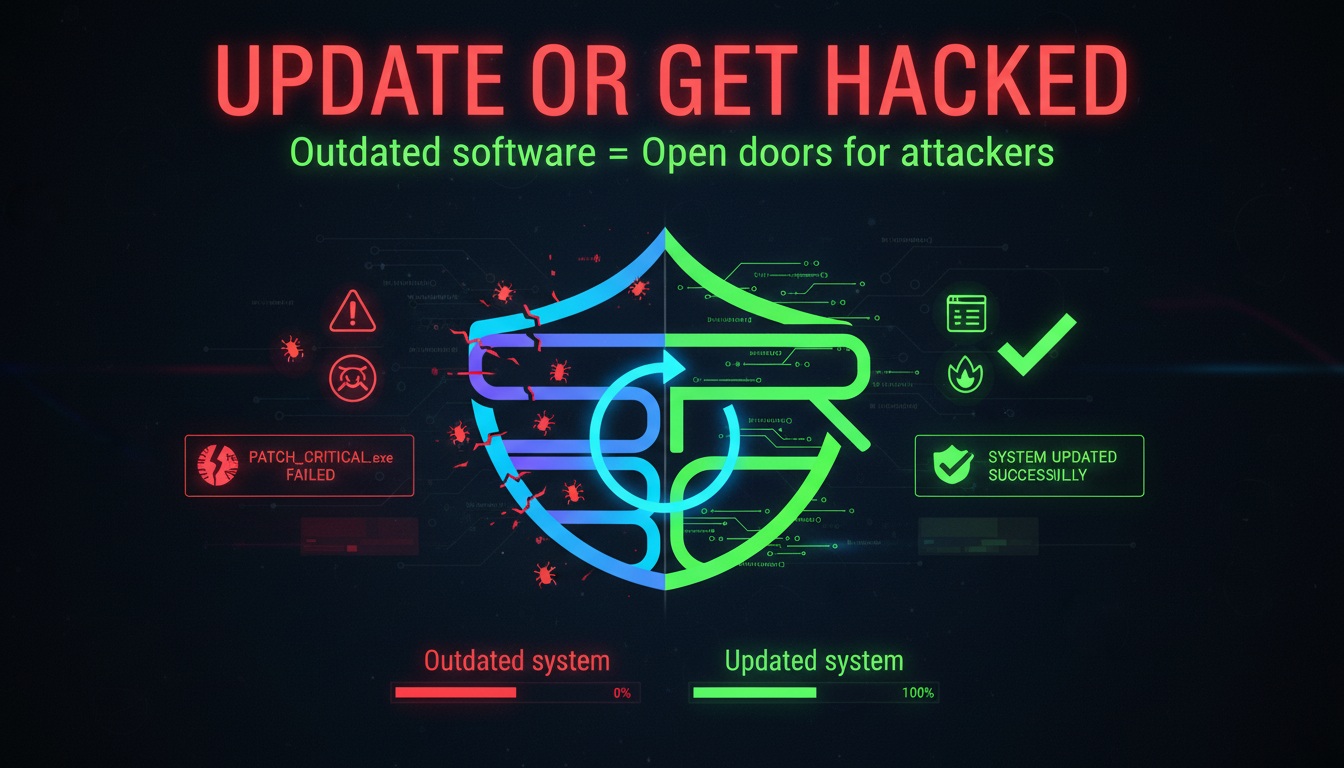
🔐 Security Software & Updates Keeping your devices secure isn’t just about installing antivirus software—it’s about keeping everything up to date. Cybercriminals are constantly searching for ...