From Victim to Defender: How Cyber Attacks Really Work (Step-by-Step Guide)
Learn how cyber attacks actually work step-by-step. A beginner-friendly cybersecurity guide to understand hackers and protect yourself online.
Learn how cyber attacks actually work step-by-step. A beginner-friendly cybersecurity guide to understand hackers and protect yourself online.

🆓 Top Free Cybersecurity Resources Cybersecurity education doesn’t have to be expensive. In fact, some of the best learning platforms, tools, and communities are completely free. At ASRBD, we bel...
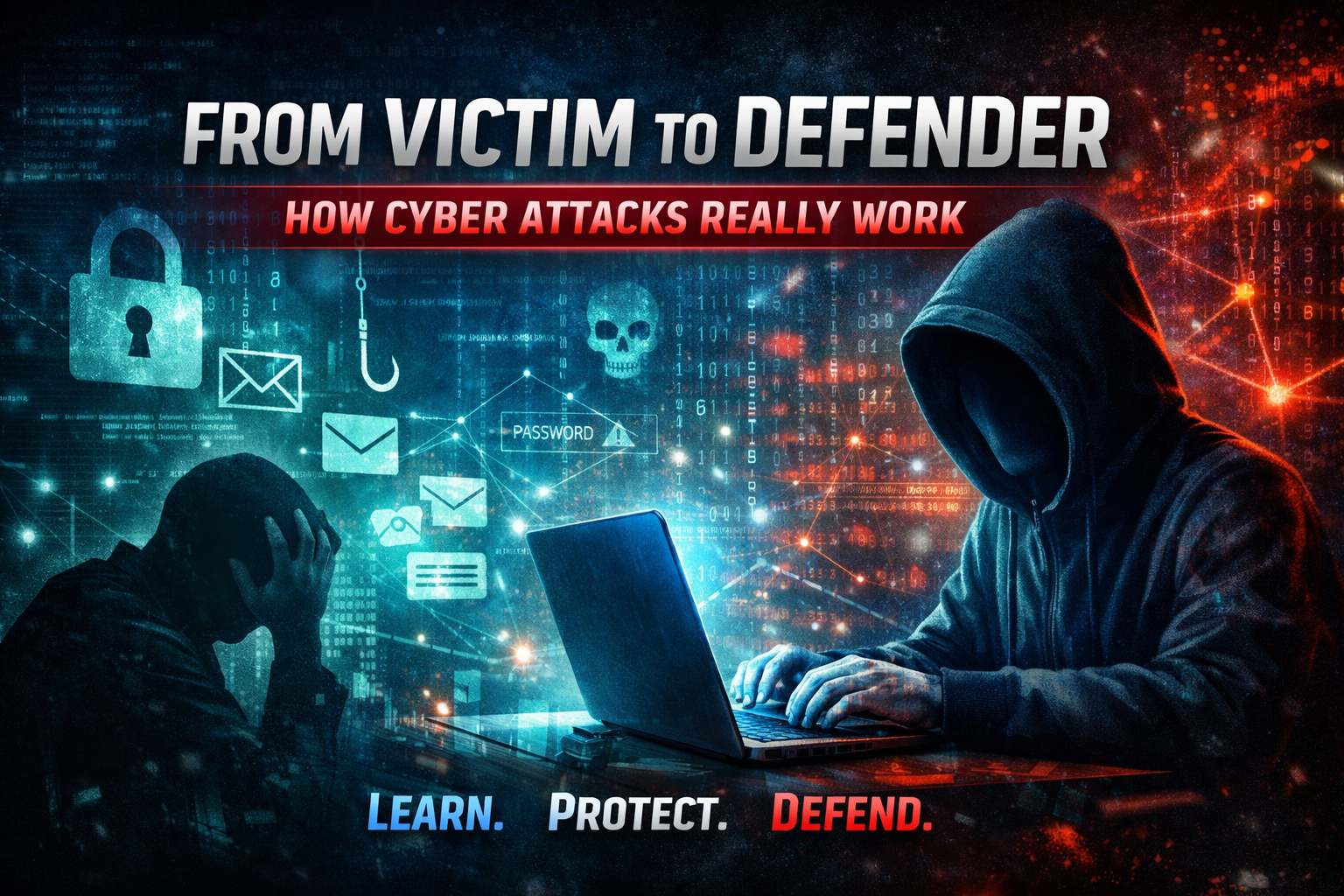
🛡️ Cybersecurity Learning Roadmap Cybersecurity is one of the most critical and in-demand fields in the modern digital era. Whether you are a student, IT enthusiast, or aspiring ethical hacker, ha...

Data privacy starts with one simple habit: checking what your apps can access. Many mobile and desktop apps request permissions for camera, microphone, contacts, location, storage, SMS, and files....

🔐 Secure Social Media in 5 Minutes You use social media every day. But is it secure? Platforms like Facebook, Instagram, and others store your: Personal data Conversations Photos Busine...
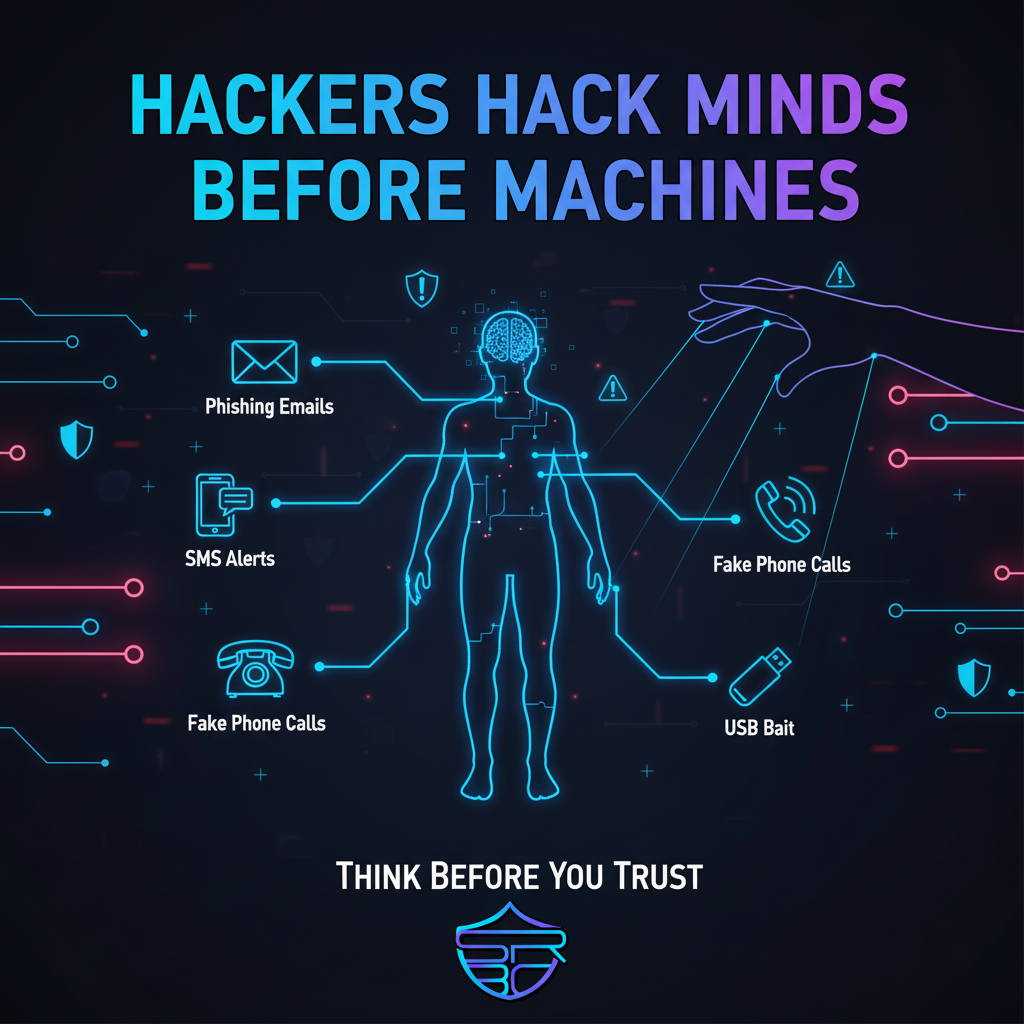
Social engineering is one of the most dangerous cyberattack methods because it targets people instead of systems. Attackers manipulate human psychology using fear, urgency, trust, curiosity, or re...

🔐 2FA vs SMS: Use Authenticator Apps Instead You enabled Two-Factor Authentication (2FA). That’s a great step. But if you’re still using SMS codes, your accounts may not be as secure as you think...

Browser and app settings are often the first line of defense for your privacy and digital safety. Many users install browsers and mobile apps but never review the default settings. This can leave ...

🔐 Build an Unhackable Password Strategy Most cyberattacks don’t start with advanced hacking tools. They start with weak passwords. Your password is the first line of defense protecting your digi...

Remote work has transformed how people collaborate, allowing teams to stay productive from home, cafés, or while traveling. However, this flexibility also introduces new cybersecurity risks that ca...