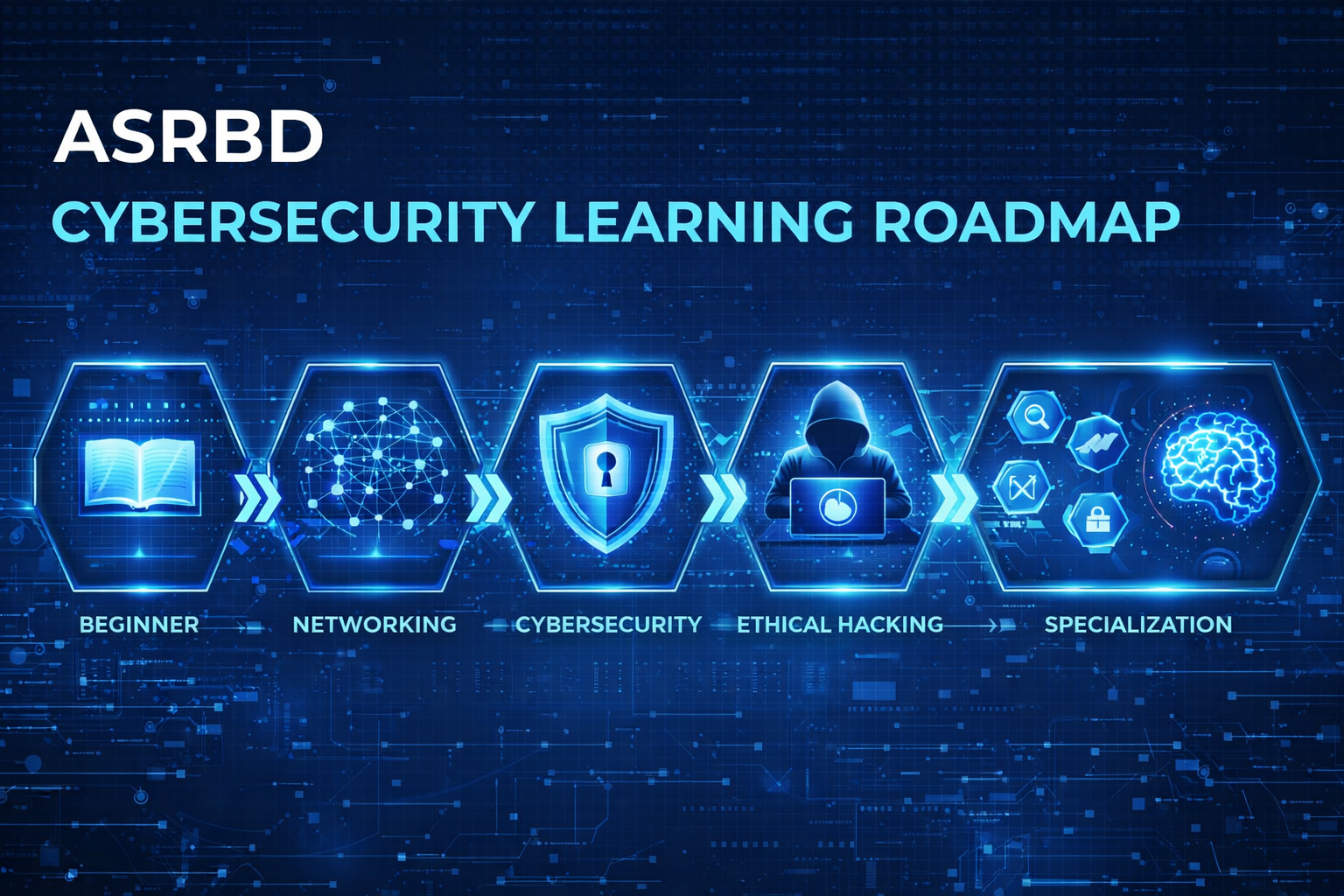
Cybersecurity Learning Roadmap 2026: From Beginner to Expert
🛡️ Cybersecurity Learning Roadmap
Cybersecurity is one of the most critical and in-demand fields in the modern digital era. Whether you are a student, IT enthusiast, or aspiring ethical hacker, having a structured roadmap is essential to mastering this domain.
This guide by ASRBD (Advanced Cybersecurity Researchers Bangladesh) provides a step-by-step roadmap to help you go from beginner to expert.
🎯 Stage 1: Build the Foundation (Beginner Level)
Before diving into hacking or security tools, you must understand the basics of how systems work.
📚 Core Topics:
- Computer Fundamentals
- Operating Systems (Windows & Linux)
- Networking Basics (IP, DNS, HTTP/HTTPS)
- Internet Architecture
🧠 What to Learn:
- How data travels across networks
- Basic command line usage (Linux terminal)
- File systems and permissions
🛠️ Tools to Start:
- Linux (Ubuntu / Kali Linux)
- VirtualBox or VMware
🌐 Stage 2: Networking & System Understanding
Cybersecurity heavily relies on networking knowledge.
📚 Core Topics:
- TCP/IP Model
- Subnetting & Routing
- Firewalls & NAT
- DNS, DHCP
🧠 Skills:
- Analyze network traffic
- Understand ports and protocols
- Configure basic networks
🛠️ Tools:
- Wireshark
- Nmap
🔐 Stage 3: Core Cybersecurity Concepts
Now step into the actual world of cybersecurity.
📚 Topics:
- CIA Triad (Confidentiality, Integrity, Availability)
- Cryptography Basics
- Authentication & Authorization
- Common Threats (Phishing, Malware, Ransomware)
🧠 Skills:
- Risk assessment
- Identifying vulnerabilities
- Understanding attack vectors
💻 Stage 4: Practical Skills & Ethical Hacking
This is where theory meets real-world application.
📚 Topics:
- Web Security (OWASP Top 10)
- SQL Injection, XSS, CSRF
- Password Attacks
- Social Engineering
🛠️ Tools:
- Burp Suite
- Metasploit
- John the Ripper
🧠 Practice Platforms:
- TryHackMe
- Hack The Box
🔍 Stage 5: Specialization Paths
Choose your path based on your interest:
🕵️ Digital Forensics
- Evidence Collection
- Disk & Memory Analysis
- Tools: Autopsy, FTK
🛡️ Blue Team (Defense)
- SIEM Tools
- Threat Monitoring
- Incident Response
⚔️ Red Team (Offense)
- Penetration Testing
- Exploit Development
- Advanced Recon
☁️ Cloud Security
- AWS / Azure Security
- Identity & Access Management
📈 Stage 6: Advanced & Professional Level
📚 Topics:
- Reverse Engineering
- Malware Analysis
- Zero-Day Research
- Threat Intelligence
🧠 Skills:
- Writing exploits
- Advanced scripting (Python, Bash)
- Automation in security
🏆 Certifications to Consider
- CompTIA Security+
- CEH (Certified Ethical Hacker)
- eJPT / eCPPT
- OSCP (Advanced Level)
📅 Suggested Learning Timeline
| Stage | Duration |
|---|---|
| Beginner | 1–2 Months |
| Networking | 2–3 Months |
| Core Security | 2 Months |
| Practical Hacking | 3–6 Months |
| Specialization | Ongoing |
💡 Tips for Success
- Stay consistent (learn daily)
- Practice more than theory
- Join cybersecurity communities
- Follow real-world case studies
- Build your own lab
🌍 Learn with ASRBD
At ASRBD, we are committed to building a skilled, ethical, and aware cybersecurity community in Bangladesh.
Our Knowledge Base, guides, and awareness programs are designed to help you:
- Learn cybersecurity step-by-step
- Gain practical experience
- Contribute to digital safety
🚀 Final Words
Cybersecurity is not just a career — it’s a responsibility.
With the right roadmap, dedication, and ethical mindset, you can become a part of the next generation of cybersecurity defenders.