Day 25 - Insider Threat Awareness
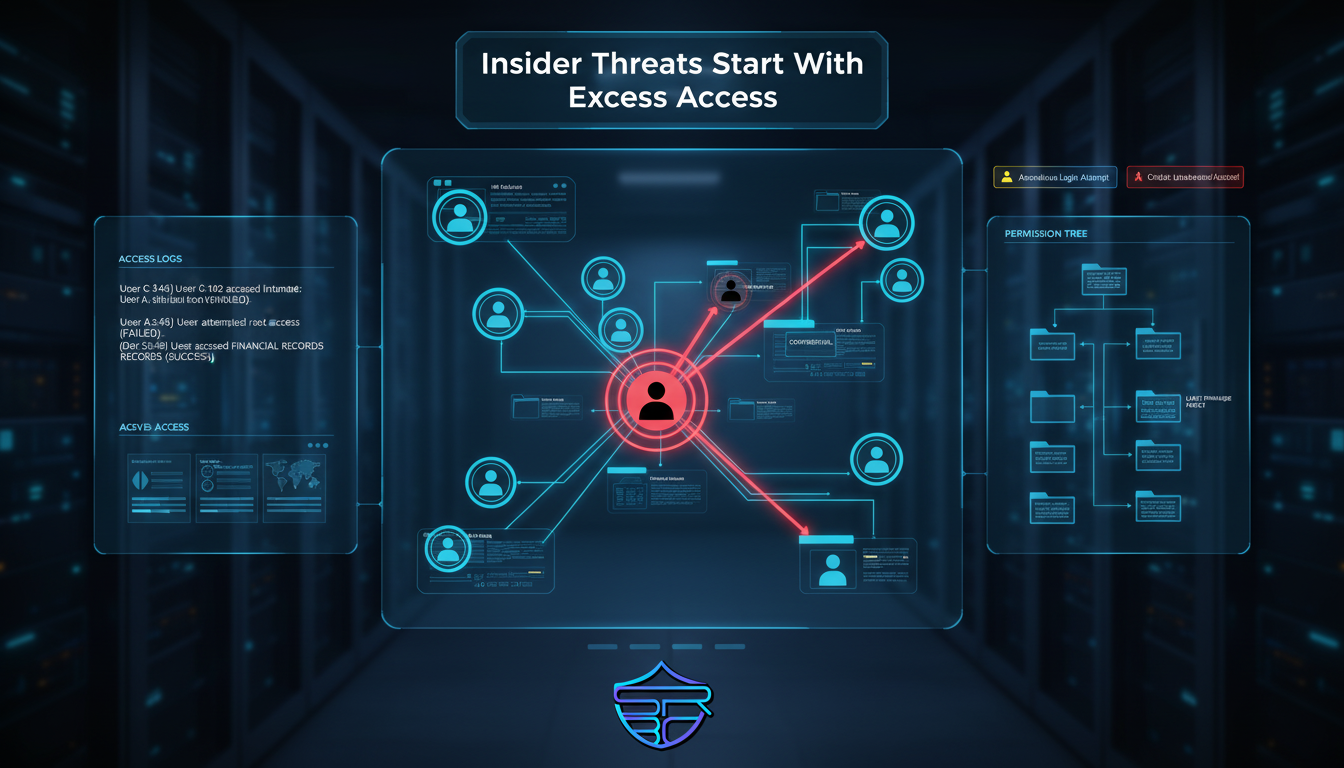
Insider threats are among the most overlooked cybersecurity risks because the danger often comes from trusted access.
Unlike external hackers, insiders already have legitimate credentials, system permissions, and knowledge of internal workflows.
This makes insider incidents more difficult to identify and often more harmful.
Common Types of Insider Threats
- Negligent employees accidentally exposing data
- Malicious insiders stealing or deleting sensitive information
- Compromised employee credentials
- Vendors or contractors with unnecessary access
- Former staff accounts left active
How to Reduce Insider Threats
1) Apply Least Privilege
Users should only have access to the systems and data required for their job.
2) Monitor User Activity
Watch for unusual file access, mass downloads, odd login times, and privilege escalation attempts.
3) Revoke Access Immediately
When staff leave roles or organizations, disable accounts and recover devices immediately.
4) Review Third-Party Access
Audit vendors, contractors, and service accounts regularly.
5) Build Reporting Culture
Encourage teams to report suspicious requests, unusual behavior, or access misuse.
Key Takeaway
Strong cybersecurity is not only about stopping external hackers.
It is also about controlling trusted access, monitoring misuse, and enforcing least privilege.
Security starts with visibility, accountability, and access control.
Stay aware. Stay protected. Stay with ASRBD.
Follow ASRBD for more cybersecurity related content