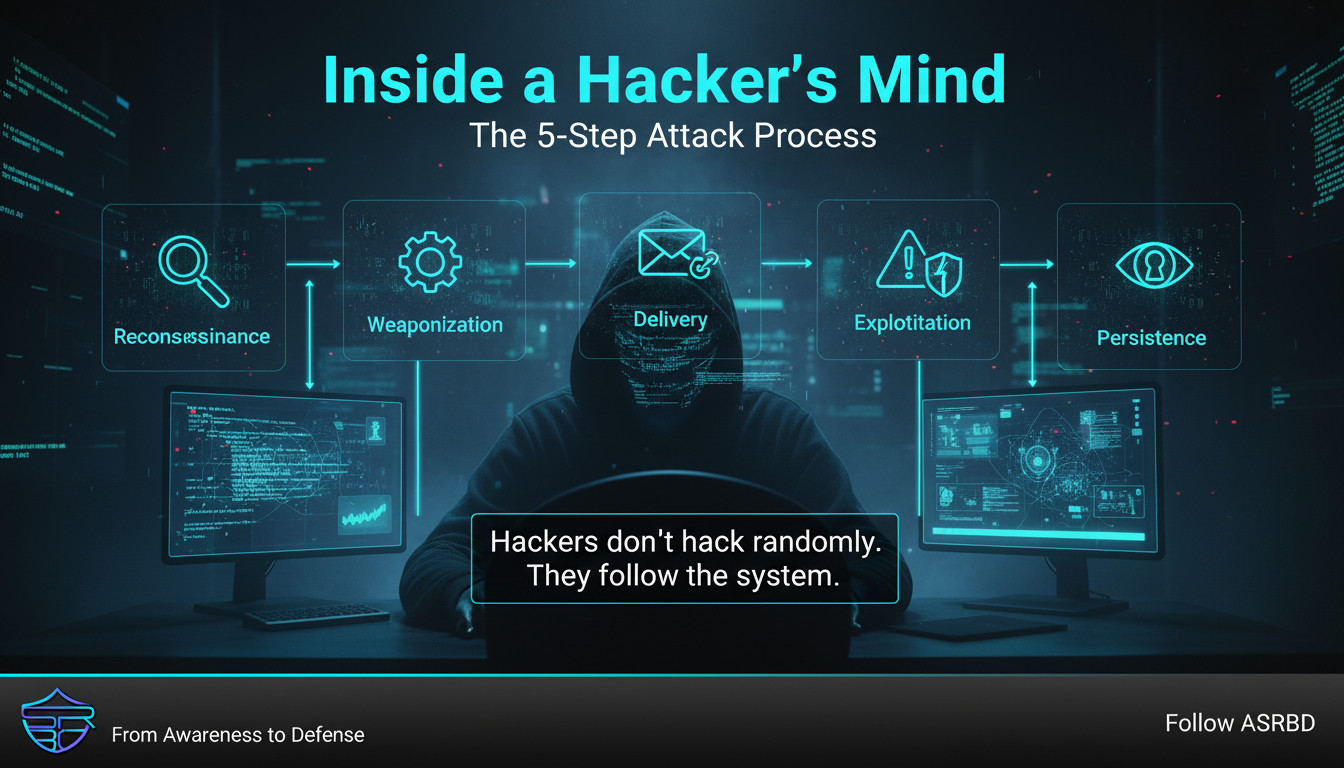
Inside a Hacker’s Mind: The 5-Step Attack Process
🧠 Inside a Hacker’s Mind
Most people think hacking is random, chaotic, and unpredictable.
But in reality?
Hackers follow a structured playbook.
Understanding this process is the first step to stopping an attack before it even begins.
🔍 The 5-Step Attack Process
1. Reconnaissance (Information Gathering)
Every attack starts with research.
Hackers collect:
- Email addresses
- Social media data
- Organization details
- Technologies in use
Even small pieces of information can be used to build a targeted attack.
2. Weaponization
Once enough data is gathered, attackers prepare their tools.
This may include:
- Malicious documents (PDF, DOCX)
- Fake login pages
- Embedded malware
At this stage, information is turned into a weapon.
3. Delivery
Now the attack is sent to the target.
Common methods:
- Phishing emails
- Malicious links
- Compromised websites
- Infected USB devices
This is where human behavior is heavily targeted.
4. Exploitation
This is the point of entry.
If the victim:
- Clicks a malicious link
- Downloads an infected file
- Enters credentials on a fake page
The attacker gains access.
Sometimes, a single click is enough.
5. Persistence
After gaining access, attackers aim to stay hidden.
They may:
- Install backdoors
- Create hidden accounts
- Maintain long-term system access
This allows them to monitor, steal data, or control systems over time.
⚠️ Why This Matters
Most people only notice an attack after damage is done.
But the truth is:
Every stage is an opportunity to stop the attacker.
- Limit oversharing → Stop reconnaissance
- Verify files → Stop weaponization
- Avoid suspicious links → Stop delivery
- Stay cautious → Stop exploitation
- Monitor systems → Stop persistence
🛡️ Final Thoughts
Hackers don’t rely on luck.
They rely on process.
If you understand that process, you can move from being a target to being prepared.
🚀 Stay Secure
Follow ASRBD (Advanced Security Researchers Bangladesh) for more real-world cybersecurity insights, attack breakdowns, and defense strategies.
Stay aware. Stay secure.